management, moving beyond manual and memory-based account (ID
/password) practices to address the increasing risk of password-related
security incidents caused by internal and external threats, while
ensuring compliance with strengthened security regulations and requirements.



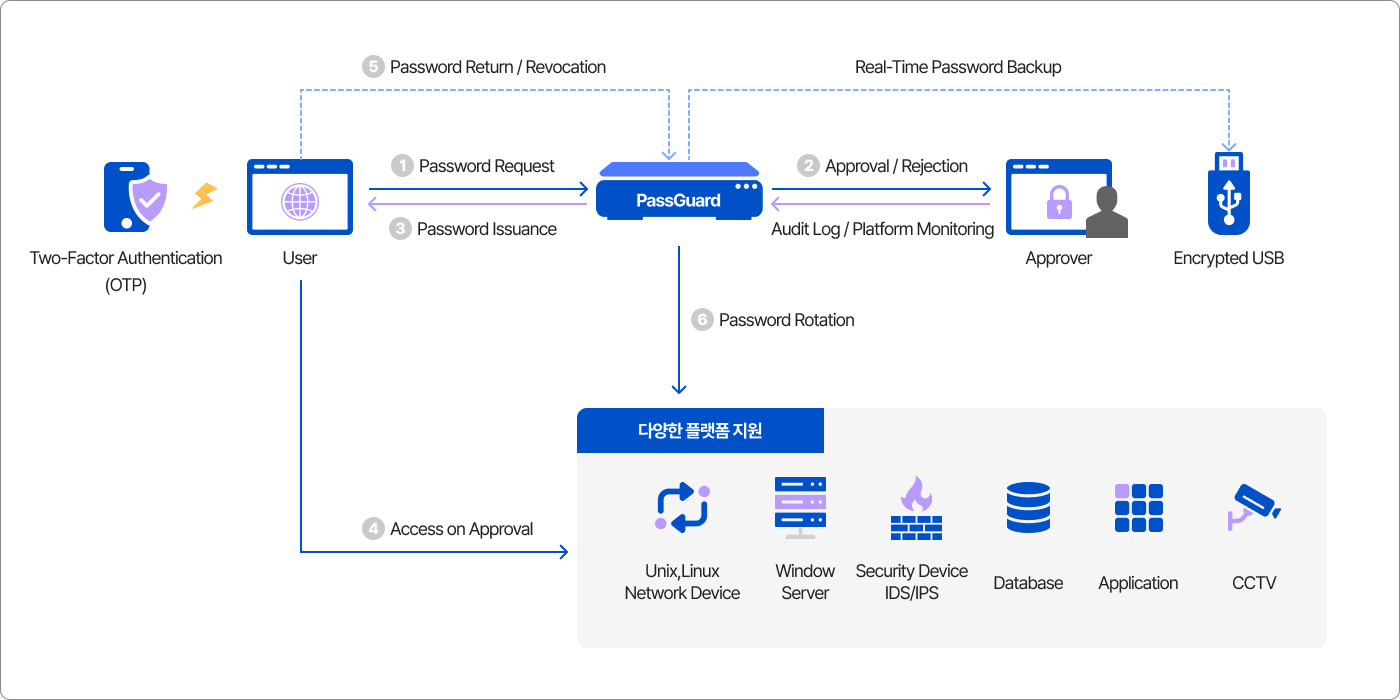
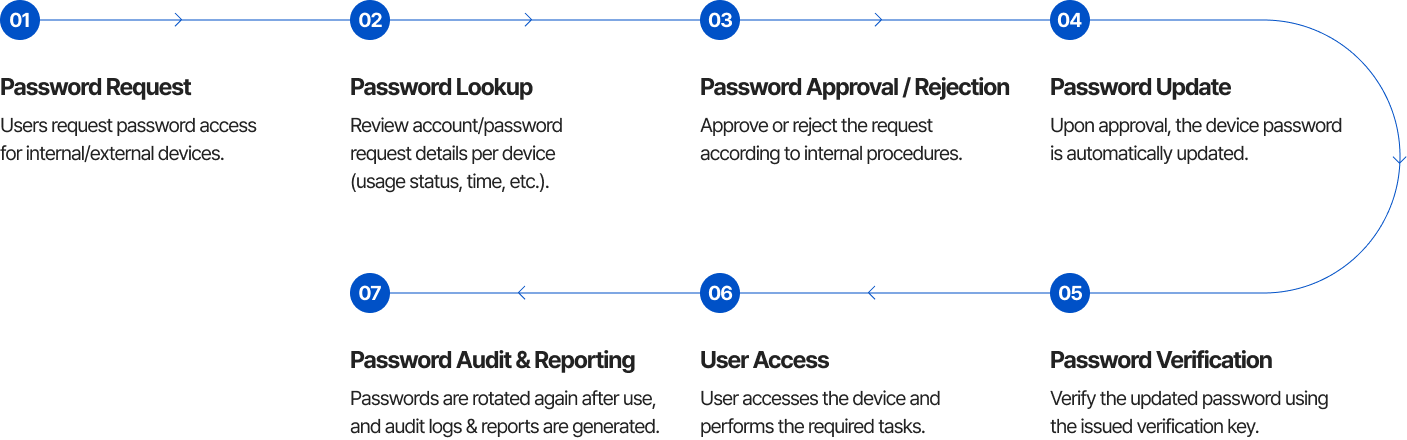
- Request and approval workflow for platform account permissions
- Pre-approval and post-approval process support
- Return and revocation of account access by users or administrators
- Comprehensive audit reports for permission requests, password queries, and changes
- No agent or additional software installation required on customer systems
- Password management and rotation provided through a fully web-based solution
- Linux, Unix, Windows accounts, and DBMS
- Security appliances, network devices, applications, and CCTV systems
- Two-factor authentication (OTP)
- IP/MAC-based access control policies
- One-way encryption for password storage
- Session timeout options based on user attributes
- Physical security controls (drive bay locking, SED HDD)
- Redundant paths for power, NIC, and storage
- High-availability architecture with no downtime (Master/Slave, Active-Active)
- Tertiary backup capability using secure removable storage



